CounterPunch bracht afgelopen woensdag een
artikel waarin gehakt wordt gemaakt van de bewering dat Noord-Korea
achter de WannaCry ‘cyberaanval’ zou zitten……. Homeland
Security (DHS) adviseur Tom Bossart kwam een paar weken geleden met deze waanzinnige claim (op 19 december 2017). Met deze claim moet het publiek nog verder worden opgezweept in de richting van een (illegale) oorlog tegen Noord-Korea…….
Bewijzen werden weer niet geleverd,
sterker nog: Gregory Elich, de schrijver van het hierna opgenomen
artikel toont middels een indrukwekkend aantal feiten aan dat
Noord-Korea niet achter deze cyberaanval kan zitten, zoals
Noord-Korea ook de Sony hack niet heeft uitgevoerd, de hack waarbij
Contopee malware werd gebruikt door de Lazarus Group….
Zoals eerder gesteld: het is duidelijk dat de Trump
administratie Noord-Korea zoveel mogelijk in een kwaad daglicht wil
stellen en ook deze beschuldiging is gericht op het angst- en
haatzaaien voor resp. tegen Noord-Korea……
De landen die het meest getroffen werden door WannaCry waren Rusland en China; waarom zou Noord-Korea deze landen aanvallen, het gaat immers om de laatste landen die het nog opnemen voor Noord-Korea??!!!
Het is even een zit, maar daarna zal
niemand je nog overtuigen dat Noord-Korea achter WannaCry zit:

Photo by Blogtrepreneur | CC BY 2.0
by GREGORY
ELICHJANUARY
3, 2018
On
December 19, in a Wall Street Journal editorial that drew much
attention, Homeland Security Advisor Tom Bossert asserted that North
Korea was “directly responsible” for the WannaCry cyberattack
that struck more than 300,000 computers worldwide. The virus
encrypted files on infected computers and demanded payment in return
for supposedly providing a decryption key to allow users to regain
access to locked files. Bossert charged that North Korea was “using
cyberattacks to fund its reckless behavior and cause disruption
across the world.” [1]
At
a press conference on the same day, Bossert announced that the
attribution was made “with evidence,” and that WannaCry “was
directed by the government of North Korea,” and carried out by
“actors on their behalf, intermediaries.” [2] The
evidence that led the U.S. to that conclusion? Bossert was not
saying, perhaps recalling the ridicule that greeted the FBI and
Department of Homeland Security’s misbegotten report on the hacking
of the Democratic National Committee.
The
centerpiece of the claim of North Korean culpability is the
similarity in code between the Contopee malware, which opens backdoor
access to an infected computer, and code in an early variant of
WannaCry. [3]
Contopee
has been linked to the Lazarus group, a cybercrime organization that
some believe launched the Sony hack, based on the software tools used
in that attack. Since North Korea is widely considered to be behind
the cyberattack on Sony, at first glance that would appear to seal
the argument.
It
is a logical argument, but is it founded on valid premises? Little is
known about Lazarus, aside from the operations that are attributed to
it. The link between Lazarus and North Korea is a hypothesis based on
limited evidence. It may or may not be true, but the apparent linkage
is far weaker than mainstream media’s conviction would have one
believe. Lazarus appears to be an independent organization possibly
based in China, which North Korea may or may not have contracted to
perform certain operations. That does not necessarily mean that every
action – or even any action at all – Lazarus performs is at North
Korea’s behest.
In
Bossert’s mind as well as that of media reporters, Lazarus – the
intermediaries Bossert refers to – and North Korea are synonymous
when it comes to cyber operations. North Korea gives the orders and
Lazarus carries them out. James Scott, a senior fellow at the
Institute for Critical Infrastructure Technology, notes that
“speculation concerning WannaCry attributes the malware to the
Lazarus Group, not to North Korea, and even those connections are
premature and not wholly convincing. Lazarus itself has never been
definitively proven to be a North Korean state-sponsored advanced
persistent threat (APT); in fact, an abundance of evidence suggests
that the Lazarus group may be a sophisticated, well-resourced, and
expansive cyber-criminal and occasional cyber-mercenary collective.”
Furthermore, Scott adds, the evidence used to tie Lazarus to North
Korea, “such as an IP hop or some language indicators, are
circumstantial and could even be intentional false flags” to
misdirect investigators. [4]
Whether
an association exists or not between Lazarus and North Korea has
little meaning regarding a specific attack. Joseph Carson of Thycotic
emphasizes “that it is important to be clear that [Lazarus] is a
group and motives can change depending on who is paying. I have found
when researching hacking groups they can one day be working for one
government under one alias and another using a different alias. This
means that association in cyberspace means nothing.” [5]
It
is considered a particularly damning piece of evidence that some of
the tools used in an early variant of WannaCry share characteristics
with those deployed in the cyberattack on Sony. [6] However,
there is ample cause for doubting North Korea’s role in the Sony
hack, as I have written about before. [7] Following
the Sony breach, IT businessman John McAfee revealed that he had
contact with the group that attacked Sony. “It has to do with a
group of hackers” motivated by dislike of the movie industry’s
“controlling the content of art,” he said, and the FBI was wrong
in attributing the attack to North Korea. [8]
If
attribution of the Sony hack to North Korea does not hold up, then
linkage based on tool usage falls apart.
Once
malware is deployed, it often appears for sale on the Dark Web, where
it can be purchased by cybercriminals. The reuse of code is a
time-saving measure in building new threats. Indeed, malware can find
its way onto the market quite rapidly, and almost as soon as WannaCry
was wreaking havoc back in May, it was reported that “researchers
are already finding variants” of WannaCry “in the wild.” [9]
According
to Peter Stephenson of SC Media, “The most prevailing [theory] uses
blocks of code that were part of known Korean hacks appearing in the
WannaCry code as justification for pinning the attacks on NK. That’s
really not enough. These blocks of code are readily available in the
underground and get reused regularly.” [10]
Commonality
of tool usage means less than we are led to believe. “While malware
may initially be developed and used by a single actor,” Digital
Shadows explains, “this does not mean that it will permanently
remain unique to that actor. Malware samples might be accidentally or
intentionally leaked, stolen, sold, or used in independent operations
by individual members of the group.” [11]
“Shared
code is not the same as attribution. Code can be rewritten and erased
by anyone, and shared code is often reused,” observes Patrick
Howell O’Neill of Cyberscoop. “The same technique could
potentially be used to frame another group as responsible for a hack
but, despite a lot of recent speculation, there is no definitive
proof.” [12]
None
of the shared code was present in WannaCry’s widespread attack on
May 12. Although it is more likely than not that the same actor was
behind the early variants of WannaCry and the May version, it is not
certain. Alan Woodward, cybersecurity advisor to Europol, points out,
“It is quite possible for even a relatively inexperienced group to
obtain the malicious WannaCry payload and to have repackaged this.
Hence, the only thing actually tying the May attacks to the earlier
WannaCry attacks is the payload, which criminals often copy.” [13]
The
most devastating component WannaCry utilized in its May 12 attack is
EternalBlue, an exploit of Windows vulnerabilities that was developed
by the National Security Agency and leaked by Shadow Brokers. The NSA
informed Microsoft of the vulnerability only after it learned of the
software’s theft. According to Bossert, the NSA informs software
manufacturers about 90 percent of the time when it discovers a
vulnerability in operating software. It keeps quiet about the
remaining ten percent so that it can “use those vulnerabilities to
develop exploits for the purpose of national security for the
classified work we do.” [14] Plainly
put, the NSA intentionally leaves individuals and organizations
worldwide exposed to potential security breaches so that it can
conduct its own cyber operations. This is less than reassuring.
The
May variant of WannaCry also implemented DoublePulsar, which is a
backdoor implant developed by the NSA that allows an attacker to gain
full control over a system and load executable malware.
The
two NSA-developed components are what allowed WannaCry to turn
virulent last May. After loading, EternalBlue proceeds to infect
every other vulnerable computer on the same network. It
simultaneously generates many thousands of random IP addresses and
launches 128 threads at two-second intervals, seeking vulnerabilities
in computers that it can exploit at each one of the generated
external IP addresses.[15]
China
and Russia were among the nations that were most negatively impacted
by the malware. [16] WannaCry
initially targeted Russian systems, which would seem an odd thing for
North Korea to do, given that Russia and China are the closest things
it has to allies. [17]
Digital
Shadows reports that “the malware appeared to spread virtually
indiscriminately with no control by its operators,” and a more
targeted approach “would have been more consistent with the
activities of a sophisticated criminal outfit or a
technically-competent nation-state actor.” [18]
Flashpoint
analyzed the ransom note that appeared on infected computers. There
were two Chinese versions and an English version. The Chinese texts
were written by someone who is fluent, and the English by someone
with a strong but imperfect command of English. Ransom notes in other
languages were apparently translated from the English version using
Google translator. [19] It
has been pointed out that this fact does not disprove the U.S.
attribution of North Korea, as that nation could have hired Chinese
cybercriminals. True enough, but then North Korea does not have a
unique ability to do so. If so inclined, anyone could contract
Chinese malware developers. Or cybercriminals could act on
their own.
Lazarus
and North Korean cyber actors have a reputation for developing
sophisticated code. The hallmark of WannaCry, however, is its sheer
sloppiness, necessitating the release of a series of new versions in
fairly quick succession. Alan Woodward believes that WannaCry’s
poorly designed code reveals that it had been written by “a less
than experienced malware developer.” [20]
Important
aspects of the code were so badly bungled that it is difficult to
imagine how any serious organization could be responsible.
IT
security specialists use virtual machines, or sandboxes, to safely
test and analyze malware code. A well-designed piece of malware will
include logic to detect the type of environment it is executing in
and alter its performance in a virtual machine (VM) environment to
appear benign. WannaCry was notably lacking in that regard.
“The authors did not appear to be concerned with thwarting
analysis, as the samples analyzed have contained little if any
obfuscation, anti-debugging, or VM-aware code,” notes LogRhythm
Labs. [21]
James
Scott argues that “every WannaCry attack has lacked the stealth,
sophistication, and resources characteristic of [Lazarus sub-group]
Bluenoroff itself or Lazarus as a whole. If either were behind
WannaCry, the attacks likely would have been more targeted, had more
of an impact, would have been persistent, would have been more
sophisticated, and would have garnered significantly greater
profits.” The EternalBlue exploit was too valuable to waste “on a
prolific and unprofitable campaign” like the May 12 WannaCry
attack. By contrast, Bluenoroff “prefers to silently integrate into
processes, extort them, and invisibly disappear after stealing
massive fiscal gains.” [22]Bogdan
Botezatu of Bitdefender, agrees. “The attack wasn’t targeted and
there was no clear gain for them. It’s doubtful they would use such
a powerful exploit for anything else but espionage.” [23]
WannaCry
included a “kill switch,” apparently intended as a poorly thought
out anti-VM feature. “For the life of me,” comments Peter
Stephenson, “I can’t see why they might think that would
work.” [24]When
the software executes it first attempts to connect to a hostname that
was unregistered. The malware would proceed to run if the domain was
not valid. A cybersecurity researcher managed to disable WannaCry by
registering the domain through NameCheap.com, shutting down with ease
the ability of WannaCry to infect any further computers. [25]
Once
WannaCry infected a computer, it demanded a ransom of $300 in bitcoin
to release the files it had encrypted. After three days, the price
doubled. The whole point of WannaCry was to generate income, and it
is here where the code was most inept.
Ideally,
ransomware like WannaCry would use a new account number for each
infected computer, to better ensure anonymity. Instead, WannaCry
hard-coded just three account numbers, which basically informed
authorities what accounts to monitor. [26] It
is an astonishing botch.
Incredibly,
WannaCry lacked the capability of automatically identifying which
victims paid the ransom. That meant that determining the source of
each payment required manual effort, a daunting task given the number
of infected computers. [27]Inevitably,
decryption keys were not sent to paying victims and once the word got
out, there was no motivation for anyone else to pay.
In
James Scott’s assessment, “The WannaCry attack attracted very
high publicity and very high law-enforcement visibility while
inflicting arguably the least amount of damage a similar campaign
that size could cause and garnering profits lower than even the most
rudimentary script kiddie attacks.” Scott was incredulous over
claims that WannaCry was a Lazarus operation. “There is no logical
rationale defending the theory that the methodical [Lazarus], known
for targeted attacks with tailored software, would suddenly launch a
global campaign dependent on barely functional ransomware.” [28]
One
would never know it from news reports, but cybersecurity attribution
is rarely absolute. Hal Berghel, of the Department of Computer
Science at the University of Nevada, comments on the “absence of
detailed strategies to provide justifiable, evidence-based
cyberattribution. There’s a reason for that: there is none. The
most we have is informed opinion.” The certainty with which
government officials and media assign blame in high-profile
cyberattacks to perceived enemies should at least raise questions.
“So whenever a politician, pundit, or executive tries to attribute
something to one group or another, our first inclination should
always be to look for signs of attribution bias, cognitive bias,
cultural bias, cognitive dissonance, and so forth. Our first
principle should be cui bono: What agendas are hidden? Whose
interests are being represented or defended? What’s the motivation
behind the statement? Where are the incentives behind the leak or
reportage? How many of the claims have been
substantiated
by independent investigators?” [29]
IT
security specialist Graham Cluley raises an important question. “I
think in the current hostile climate between USA and North Korea it’s
not unhelpful to retain some skepticism about why this claim might
have been made, and what may have motivated the claim to be made at
the present time.” [30]
To
all appearances, WannaCry was the work of amateurish developers who
got hold of NSA software that allowed the malware to spread like
wildfire, but their own code was so poorly written that it failed to
monetize the effort to any meaningful degree.
WannaCry
has its uses, though. The Trump administration’s public attribution
is “more about the administration’s message that North Korea is a
dangerous actor than it is about cybersecurity,” says Ross Rustici,
head of Intelligence Research at Cybereason. “They’re trying to
lay the groundwork for people to feel like North Korea is a threat to
the homeland.” [31] It
is part of a campaign by the administration to stampede the public
into supporting harsh measures or possibly even military action
against North Korea.
Notes:
[1] Thomas
P. Bossert, “It’s Official: North Korea is Behind WannaCry,”
Wall Street Journal,” December 19, 2017.
[2] “Press
Briefing on the Attribution of the WannaCry Malware Attack to North
Korea,” Whitehouse.gov, December 19, 2017.
[3] “WannaCry
and Lazarus Group – the Missing Link?” SecureList, May 15, 2017.
[4] James
Scott, “There’s Proof That North Korea Launched the WannaCry
Attack? Not So Fast! – A Warning Against Premature, Inconclusive,
and Distracting Attribution,” Institute for Critical Infrastructure
Technology, May 23, 2017.
[5] Eduard
Kovacs, “Industry Reactions to U.S. Blaming North Korea for
WannaCry,” Security Week, December 22, 2017.
[6] “WannaCry:
Ransomware Attacks Show Strong Links to Lazarus Group,” Symantec
Official Blog, May 22, 2017.
[7] Gregory
Elich, “Who Was Behind the Cyberattack on Sony?” Counterpunch,
December 30, 2014.
[8] David
Gilbert, Gareth Platt, “John McAfee: ‘I Know Who Hacked Sony
Pictures – and it Wasn’t North Korea,” International Business
Times, January 19, 2015.
[9] Amanda
Rousseau, “WCry/WanaCry Ransomware Technical Analysis,” Endgame,
May 14, 2017.
[10] Peter
Stephenson, “WannaCry Attribution: I’m Not Convinced Kim Dunnit,
but a Russian…”, SC Media, May 21, 2017.
[11] Digital
Shadows Analyst Team, “WannaCry: An Analysis of Competing
Hypotheses,” Digital Shadows, May 18, 2017.
[12] Patrick
Howell O’Neill, “Researchers: WannaCry Ransomware Shares Code
with North Korean Malware,” Cyberscoop, May 15, 2017.
[13] Alan
Woodward, “Attribution is Difficult – Consider All the Evidence,”
Cyber Matters, May 24, 2017.
[14] Thomas
P. Bossert, “It’s Official: North Korea is Behind WannaCry,”
Wall Street Journal,” December 19, 2017.
[15] Luke
Somerville, Abel Toro, “WannaCry Post-Outbreak Analysis,”
Forcepoint, May 16, 2017.
Sarah
Maloney, “WannaCry / WCry /WannaCrypt Attack Profile,”
Cybereason, May 16, 2017.
Rohit
Langde, “WannaCry Ransomware: A Detailed Analysis of the Attack,”
Techspective, September 26, 2017.
[16] Eduard
Kovacs, “WannaCry Does Not Fit North Korea’s Style, Interests:
Experts,” Security Week, May 19, 2017.
[17] “A
Technical Analysis of WannaCry Ransomware,” LogRhythm, May 16,
2017.
[18] Digital
Shadows Analyst Team, “WannaCry: An Analysis of Competing
Hypotheses,” Digital Shadows, May 18, 2017.
[19] Jon
Condra, John Costello, Sherman Chu, “Linguistic Analysis of
WannaCry Ransomware Messages Suggests Chinese-Speaking Authors,”
Flashpoint, May 25, 2017.
[20] Alan
Woodward, “Attribution is Difficult – Consider All the Evidence,”
Cyber Matters, May 24, 2017.
[21] Erika
Noerenberg, Andrew Costis, Nathanial Quist, “A Technical Analysis
of WannaCry Ransomware,” LogRhythm, May 16, 2017.
[22] James
Scott, “There’s Proof That North Korea Launched the WannaCry
Attack? Not So Fast! – A Warning Against Premature, Inconclusive,
and Distracting Attribution,” Institute for Critical Infrastructure
Technology, May 23, 2017.
[23] Eduard
Kovacs, “WannaCry Does Not Fit North Korea’s Style, Interests:
Experts,” Security Week, May 19, 2017.
[24] Peter
Stephenson, “WannaCry Attribution: I’m Not Convinced Kim Dunnit,
but a Russian…”, SC Media, May 21, 2017.
[25] Rohit
Langde, “WannaCry Ransomware: A Detailed Analysis of the Attack,”
Techspective, September 26, 2017.
[26] Jesse
Dunietz, “The Imperfect Crime: How the WannaCry Hackers Could Get
Nabbed,” Scientific American, August 16, 2017.
[27] Andy
Greenberg, “The WannaCry Ransomware Hackers Made Some Major
Mistakes,” Wired, May 15, 2017.
[28] James
Scott, “WannaCry Ransomware & the Perils of Shoddy Attribution:
It’s the Russians! No Wait, it’s the North Koreans!” Institute
for Critical Infrastructure Technology, May 18, 2017.
[29] Hal
Berghel, “On the Problem of (Cyber) Attribution,” Computer —
IEEE Computer Society, March 2017.
[30] Scott
Carey, “Should We Believe the White House When it Says North Korea
is Behind WannaCry?” Computer World, December 20, 2017.
[31] John
P. Mello Jr., “US Fingers North Korea for WannaCry Epidemic,”
Tech News World, December 20, 2017.
===================================
Zie ook: ‘False flag terror’ bestaat wel degelijk: bekentenissen en feiten over heel smerige zaken……….‘
en: ‘CIA de ware hacker en manipulator van verkiezingen, ofwel de laatste Wikileaks documenten……...’
en: ‘CIA speelt zoals gewoonlijk vuil spel: uit Wikileaks documenten blijkt dat CIA zelf de verkiezingen manipuleerde, waar het Rusland van beschuldigde……..‘
en: ‘‘Russische bemoeienis’ met de Nederlandse verkiezingen….. Waaruit blijkt nu die manipulatie, gezien de verkiezingsuitslag?‘
en: ‘CIA malware voor manipulaties en spionage >> vervolg Wikileaks Vault 7‘
en: ‘Eichelsheim (MIVD) ‘waarschuwt voor agressie CIA en NAVO……….’‘
en: ‘WikiLeaks: Seth Rich Leaked Clinton Emails, Not Russia‘
en: ‘Campagne Clinton, smeriger dan gedacht…………‘ (met daarin daarin opgenomen de volgende artikelen: ‘Donna Brazile Bombshell: ‘Proof’ Hillary ‘Rigged’ Primary Against Bernie‘ en ‘Democrats in Denial After Donna Brazile Says Primary Was Rigged for Hillary‘) Hierover zal ik wellicht later vandaag nog een bericht publiceren.
en: ‘Clinton te kakken gezet: Brazile (Democratische Partij VS) draagt haar boek op aan Seth Rich, het vermoorde lid van DNC die belastende documenten lekte‘
en: ‘Murray, ex-ambassadeur van GB: de Russen hebben de VS verkiezingen niet gemanipuleerd‘
en: ‘‘Russische manipulaties uitgevoerd’ door later vermoord staflid Clintons campagneteam Seth Rich……… AIVD en MIVD moeten hiervan weten!!‘
en: ‘Obama gaf toe dat de DNC e-mails expres door de DNC werden gelekt naar Wikileaks….!!!!‘
en: ‘VS ‘democratie’ aan het werk, een onthutsende en uitermate humoristische video!‘
en: ‘Democraten VS kochten informatie over Trump >> Forgetting the ‘Dirty Dossier’ on Trump‘
en: ‘Hillary Clinton moet op de hoogte zijn geweest van aankoop Steele dossier over Trump……..‘
en: ‘Flashback: Clinton Allies Met With Ukrainian Govt Officials to Dig up Dirt on Trump During 2016 Election‘
en: ‘FBI Director Comey Leaked Trump Memos Containing Classified Information‘
en: ‘Publicly Available Evidence Doesn’t Support Russian Gov Hacking of 2016 Election‘
en: ‘Russia Is Trolling the Shit out of Hillary Clinton and the Mainstream Media‘
en: ‘CIA chef Pompeo waarschuwt voor complot van WikiLeaks om de VS op alle mogelijke manieren neer te halen……. ha! ha! ha! ha! ha! ha! ha! ha!‘
en: ‘Russische ‘hacks’ door deskundigen nogmaals als fake news doorgeprikt >> Intel Vets Challenge ‘Russia Hack’ Evidence‘
en: ‘Rusland krijgt alweer de schuld van hacken, nu van oplichters Symantec en Facebook……. ha! ha! ha! ha! ha! ha! ha!‘
en: ‘Russiagate, of: hoe de media u belazeren met verhalen over Russische bemoeienis met de VS presidentsverkiezingen……..‘
en: ‘Donna Brazile (Democratische Partij VS) draagt haar boek op aan Seth Rich, het vermoorde lid van DNC die belastende documenten lekte‘
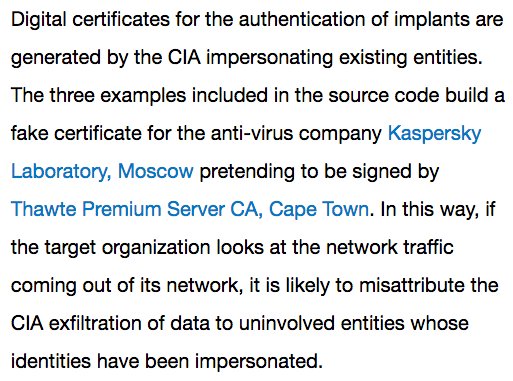
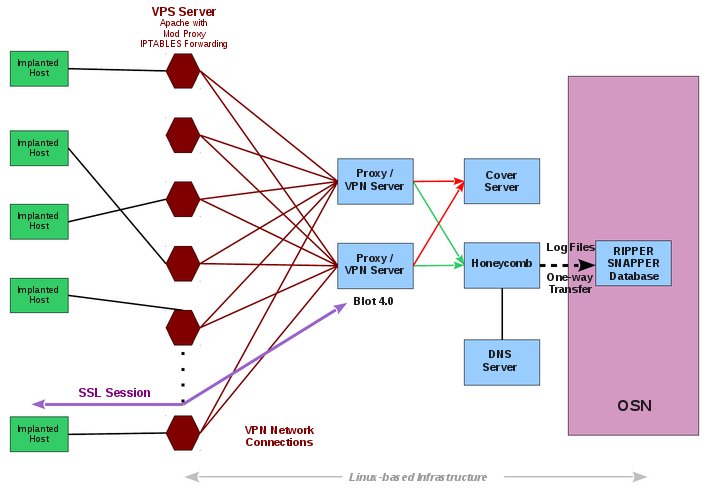
en: ‘CIA deed zich voor als het Russische Kaspersky Lab, aldus Wikileaks Vault 8…..‘